
How IT Support Companies Charge For Their Services – Part 2 Of 2
Continuing on from our previous blog post, we’re answering one of the most common questions we get[…]

Protect Your Data: Preventing Data Leaks with ChatGP
Introduction In today’s digital age, the security of personal and organizational data is paramount. With the increasing[…]

The Ultimate Guide to Managing All Your IT Requirements
In the rapidly evolving digital landscape, managing IT requirements effectively is paramount for businesses of all sizes.[…]

Cyber as a Service: Revolutionizing Cybersecurity for Modern Businesses
In the ever-evolving landscape of cybersecurity, businesses face a multitude of threats that can compromise their operations,[…]

Microsoft Sentinel
Introduction In the dynamic world of cybersecurity, the emergence of cloud-native solutions has marked a significant evolution[…]

Understanding Managed IT Services:
Ever wondered what an IT managed service team does? Managed IT services, as defined in ITIL (Information[…]

Understanding IT Outsourcing: A Comprehensive Guide
In today’s dynamic business landscape, the concept of IT outsourcing has gained significant traction, reshaping the way[…]

Audio and Visual Services
Elevating Your Business with Comprehensive Audio and Visual Support from White Arrow Technology In the modern landscape[…]

Migrate from VMWare to Cloud
Seamless Transition: A Comprehensive Guide to Migrating from VMware to the Cloud Introduction In today’s fast-paced business[…]

Unveiling WormGPT: The Dark Side of AI in Cybercrime
Introduction In the realm of artificial intelligence (AI), there exists a sinister counterpart to the benevolent ChatGPT[…]

Migrate VMware to Proxmox
Migrating from VMware to Proxmox is a process that has attracted attention among IT professionals looking to[…]

IT MSP for StartUp
Unleashing the Power of White Arrow Technology: A Comprehensive Guide for Startups Seeking IT MSP Excellence Introduction:[…]

IT MSP for Apple MAC
Unveiling the Power of White Arrow Technology: Elevating Security with IT Managed Services for Apple Mac Introduction:[…]

IT MSP for Charity
Empowering Charities: The Secure Path to Cost-Efficient IT Solutions with White Arrow Technology Introduction: In an era[…]

5 New Cybersecurity Threats You Need To Be Very Prepared For This Year
The year of 2023 marked a significant turning point for cyber-attacks with the introduction and wide proliferation[…]

Unlocking the Power of Email with GetEmail.io: A Comprehensive Review
In the dynamic landscape of business and communication, the importance of email cannot be overstated. Whether you’re[…]

Cyber Essentials
Unveiling Cyber Essentials: A Crucial Pillar in Cybersecurity Defense In an era where digital landscapes dominate, the[…]

Microsoft 365’s new AI innovations
Microsoft 365 has a powerful suite of cloud-based productivity tools. They can help you work smarter and[…]

Gamers Beware! Hackers are Targeting You.
Gamers haven’t really been the focus of cybersecurity for a long time. You mostly hear about attacks[…]

Pentest – Penetration Test
Mastering Security: The Power of Penetration Testing with White Arrow Technology In an era where digital footprints[…]
Anti-virus Bitdefender
In the dynamic landscape of cybersecurity, Managed Service Providers (MSPs) play a crucial role in safeguarding businesses[…]

WordPress plugin
Creating a WordPress plugin involves several steps, and developing one that connects to a MySQL server with[…]

IT Support
IT Support: The Role of White Arrow Technology In the realm of IT support, businesses often face[…]
The Power of Link Exchange: A Mutually Beneficial Opportunity
In today’s digital age, establishing a strong online presence is vital for businesses and individuals alike. The[…]
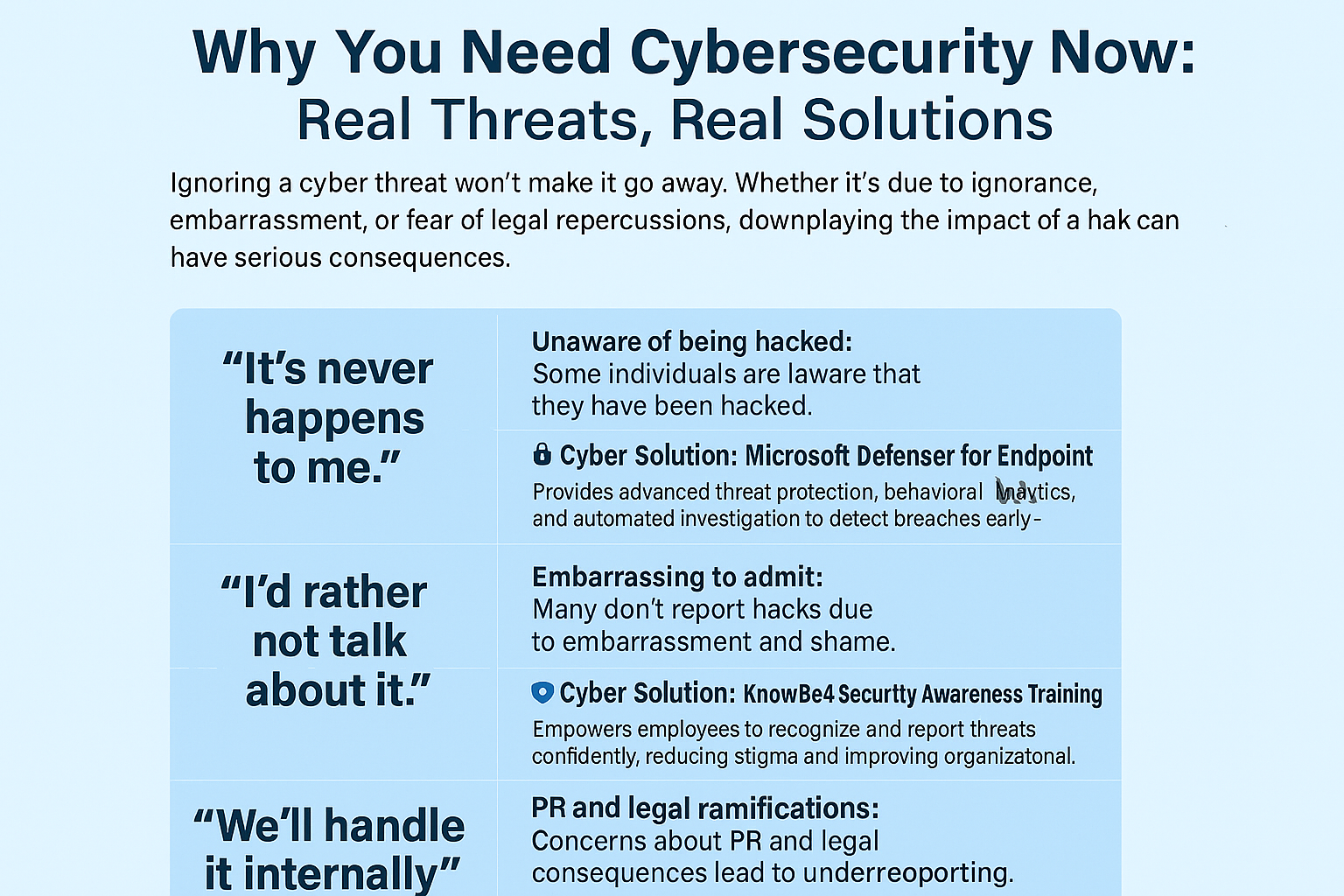
Why You Need Cybersecurity Now: Real Threats, Real Solutions
Introduction In today’s hyper-connected digital landscape, cybersecurity is no longer a technical afterthought — it’s a business-critical[…]
